Hi everyone.
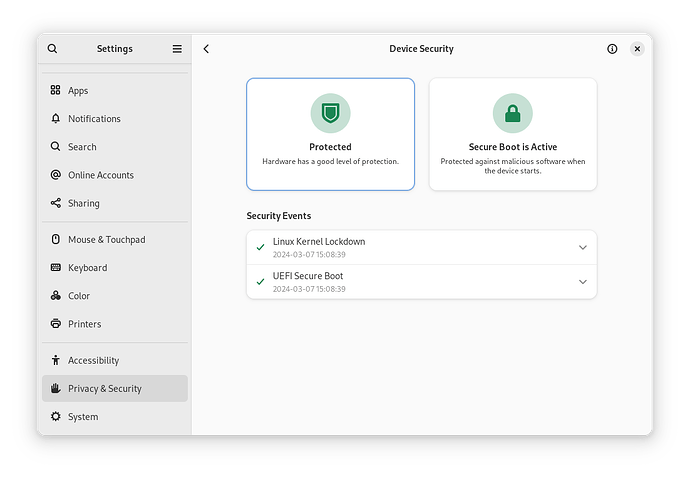
As the title suggests, I would like your opinion on how it is possible to get the status of safe device in Device Security (Settings). Although my UEFI is configured with the best safety settings (at least in my point of view), I can’t get the status of safe device.
In my humble opinion I believe that the required requirements are too many and not possible for most devices.
Thanks for your feedback.
Can you please click the “Copy Technical Report” button?
First click the button on the left. (I expect yours will be red instead of green, and say “Checks Failed.”) You might not have realized that it’s a button; it’s not clear unless you hover over it.
The Technical Report will show you exactly what is wrong.
If you’re device is more than a few years old, then yes it’s going to fail the security checks, and it won’t be possible to fix that. The device security checks have various purposes, but in my opinion the most important is to let you know whether attackers with root access to your operating system can install persistent firmware-level malware that survives even if you reinstall your OS. I think that’s a problem worth warning users about. The goal is to accurately represent your hardware security level, not ensure every user is able to get a passing security grade.
Thanks for your precious feedback and for your kind help.
No, mine is a brand new laptop.
Device Security Report
======================
Report details
Date generated: 2024-03-21 22:08:14
fwupd version: 1.9.15
System details
Hardware model: Acer Aspire AV15-51
Processor: 11th Gen Intel(R) Core(TM) i5-1155G7 @ 2.50GHz
OS: Fedora Linux 39 (Workstation Edition)
Security level: HSI:0! (v1.9.15)
HSI-1 Tests
Chiave piattaforma UEFI: Pass (Valido)
Versione Intel Management Engine: ! Fail (Non valido)
Variabili bootservice UEFI: Pass (Bloccato)
TPM v2.0: Pass (Trovato)
Regione BIOS firmware: Pass (Bloccato)
Avvio sicuro UEFI: Pass (Abilitato)
Blocco protezione scrittura firmware: Pass (Abilitato)
Debug piattaforma: Pass (Non abilitato)
Modalità costruttore Intel Management Engine: Pass (Bloccato)
BIOS Firmware Updates: Pass (Abilitato)
Protezione scrittura firmware: Pass (Non abilitato)
Configurazione piattaforma TPM: Pass (Valido)
Disabilitazione Intel Management Engine: Pass (Bloccato)
HSI-2 Tests
Debug piattaforma: Pass (Bloccato)
ACM protetto Intel BootGuard: ! Fail (Non valido)
Protezione IOMMU: ! Fail (Non trovato)
Fusibile Intel BootGuard: Pass (Valido)
Mitigazione GDS Intel: Pass (Abilitato)
Avvio verificato Intel BootGuard: ! Fail (Non valido)
Ricostruzione TPM: Pass (Valido)
Intel BootGuard: Pass (Abilitato)
HSI-3 Tests
Sospensione in RAM: Pass (Non abilitato)
Regole di errore Intel BootGuard: ! Fail (Non valido)
Protezione DMA pre-boot: Pass (Abilitato)
Control-flow Enforcement Technology: Pass (Supportato)
Sospensione: Pass (Abilitato)
HSI-4 Tests
RAM cifrata: ! Fail (Non supportato)
Supervisor Mode Access Prevention: Pass (Abilitato)
Runtime Tests
Control-flow Enforcement Technology: ! Fail (Non supportato)
Verifica aggiornamento firmware: Pass (Non contaminato)
Swap Linux: Pass (Cifrato)
Verifica kernel Linux: Pass (Non contaminato)
Lockdown kernel Linux: Pass (Abilitato)
Host security events
2023-12-12 21:57:31 Controlli di sicurezza del processoreSuperato (Non valido → Valido)
2023-12-12 21:57:31 Intel CET Superato (Abilitato → Supportato)
2023-12-12 21:27:33 Controlli di sicurezza del processoreSuperato (Valido → Non valido)
For information on the contents of this report, see https://fwupd.github.io/hsi.html
Well it might be brand new to you, but it’s three Intel generations behind. It looks like the Intel ME version check has failed. Accordingly, your device is assumed to be vulnerable to these eight CVEs from 2017. I’m not sure if it’s failing because of some bug, or if the version is known and just too old. If Acer has not distributed firmware with a newer Intel ME version, then it unfortunately won’t be possible to achieve HSI-1.
You can try installing the latest firmware updates from Acer and see if that helps. For further help, you can ask in the fwupd discussion forum.
Thanks for the clarification. The latest Acer firmware update was installed a few months ago and no others have been released. It seems strange that Acer did not provide the security patches for their firmware.
At this point, unless you have other suggestions to give me, I will try to write in the fwupd discussion forum.
You can often update the CSME firmware directly: Intel (Converged Security) Management Engine: Drivers, Firmware and Tools (2-15) - Intel Management Engine - Win-Raid Forum
That would get you HSI1
Thank you for the suggestion. It does not seem to me a particularly simple procedure.
This topic was automatically closed 30 days after the last reply. New replies are no longer allowed.